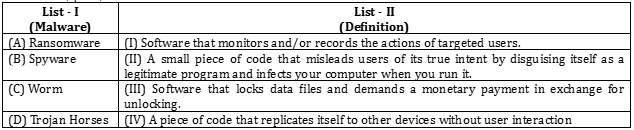
Correct option is D
A. Ransomware → III. Software that locks data files and demands a monetary payment in exchange for unlocking.
Ransomware is a type of malicious software designed to block access to a computer system or files until a sum of money is paid. It encrypts the data and demands payment from the victim to restore access.
B. Spyware → I. Software that monitors and/or records the actions of targeted users.
Spyware is designed to secretly monitor and collect data on a user’s activities, such as browsing habits or sensitive information like usernames and passwords, without their knowledge.
C. Worm → IV. A piece of code that replicates itself to other devices without user interaction.
A worm is a standalone malware program that replicates itself in order to spread to other computers. Unlike viruses, worms don't need to attach themselves to an existing program or require user action to spread.
D. Trojan Horses → II. A small piece of code that misleads users by disguising itself as a legitimate program and infects your computer when you run it.
Trojan horses appear to be useful software but carry hidden malicious code. When users download or open them, they can perform unauthorized actions such as stealing data or installing other malware.
Information Booster: ·
Ransomware: It encrypts files on a computer and asks for payment (usually in cryptocurrency) for the decryption key.
· Famous example: WannaCry attack.
·
Spyware: Can be installed by visiting untrusted websites or downloading suspicious software. It can track online behavior, keystrokes, and even capture screenshots without consent.
·
Worms: Unlike viruses, worms spread through vulnerabilities in network security.
· Famous example: Morris Worm, one of the earliest known worms.
·
Trojan Horses: A Trojan horse can provide a backdoor for malicious users, giving them control of the infected computer. It often comes disguised as a software update or an attachment in phishing emails.
·
Malware is a collective term for any software intentionally designed to cause damage or exploit a system, which includes viruses, worms, ransomware, spyware, and Trojan horses.
·
Anti-malware measures: It's essential to install reliable antivirus software, keep operating systems updated, and avoid downloading files from untrusted sources to prevent malware infections.





 English
English 10 Questions
10 Questions 12 Mins
12 Mins